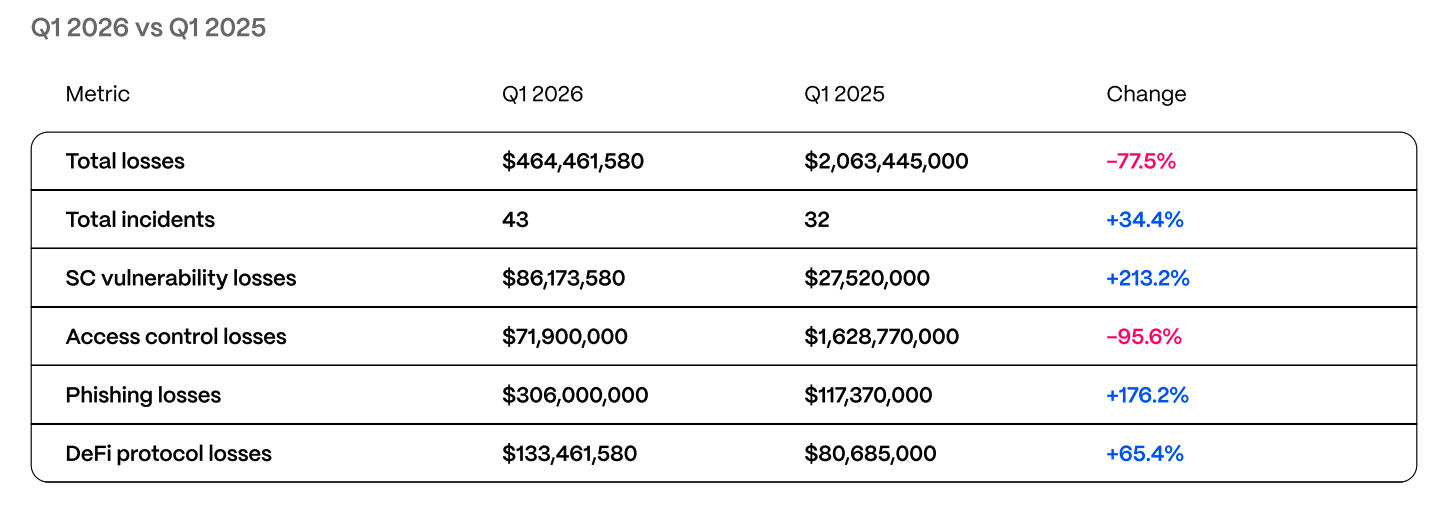
Phishing, social engineering behind $464.5M Web3 losses in Q1

Web3 projects lost $464.5 million to hacks and scams in Q1 2026. Phishing and social engineering accounted for $306 million; a $282 million hardware‑wallet scam was the largest single loss.
Web3 projects suffered $464.5 million in losses to hacks and scams in the first quarter of 2026, according to a report from blockchain security firm Hacken. Phishing and social engineering accounted for $306 million of the total. Smart contract exploits were responsible for $86.2 million, and access control failures, including compromised keys and cloud services, added $71.9 million.
Hacken recorded 43 incidents in Q1 2026 and said the quarter had fewer very large ‘‘mega hacks’’ but more mid‑sized operational failures. A January hardware‑wallet scam produced the largest single loss of the quarter.
Yev Broshevan, chief executive and co‑founder of Hacken, told reporters that “The most expensive failures happen outside the code layer entirely,” describing a shift toward losses tied to human and infrastructure factors.
The report lists several notable incidents. Step Finance lost about $40 million after what Hacken linked to a fake venture capital outreach campaign tied to North Korean actors and malicious video‑call tooling. Resolv Labs suffered roughly $25 million following a compromise of an AWS key management service. Truebit lost $26.4 million to a bug in a Solidity contract deployed about five years earlier. Venus Protocol was exploited using a donation‑style attack pattern.
Hacken said six audited projects, including Resolv and Venus, together accounted for $37.7 million in losses during the quarter. The firm noted that audited projects can still be breached.
Regulatory and institutional responses are tightening. Hacken cited enforcement and guidance from the European Union’s Markets in Crypto‑Assets Regulation and the Digital Operational Resilience Act, updated technical rules from Dubai’s Virtual Assets Regulatory Authority, Singapore’s Basel‑aligned capital requirements and one‑hour incident notification rule, and broader federal oversight under the United Arab Emirates’ new Capital Market Authority.
To meet those standards, Hacken recommended security measures it calls “regulator‑ready” stacks. These include proof‑of‑reserves attestations supported by daily internal reconciliation, continuous 24/7 on‑chain monitoring of treasury wallets and privileged roles, automated circuit‑breakers for minting and governance, and incident notification processes aligned with the strictest applicable rules. The report sets practical response targets of awareness within 24 hours, labeling within four hours, and blocking within 30 seconds, and lists aspirational goals such as detection in 10 minutes and blocking in one second.
The report also flagged activity by state‑linked groups. Hacken said North Korean clusters continued to carry out fake VC outreach, endpoint compromise and related tactics, and that those patterns contributed to about $2.04 billion in sector losses in 2025.
Hacken’s analysis stated that high‑value failures have increasingly occurred in operational and infrastructure layers that traditional smart contract audits do not always cover.
The material on GNcrypto is intended solely for informational use and must not be regarded as financial advice. We make every effort to keep the content accurate and current, but we cannot warrant its precision, completeness, or reliability. GNcrypto does not take responsibility for any mistakes, omissions, or financial losses resulting from reliance on this information. Any actions you take based on this content are done at your own risk. Always conduct independent research and seek guidance from a qualified specialist. For further details, please review our Terms, Privacy Policy and Disclaimers.